
CallShield
Voice Fraud, Voice Spam, and CLI Spoofing Protection
When security is compromised, fraud is inevitable. Fraudsters are now using artificial intelligence to change their behavior in real-time to avoid detection. Mavenir is securing voice, messaging, data and revenue protection with the Fraud and Security Suite, which provides Communications Service Providers (CSPs) a robust security strategy that protects the network and its customer base in real-time, with predictive analytics through Machine Learning (ML) technology.
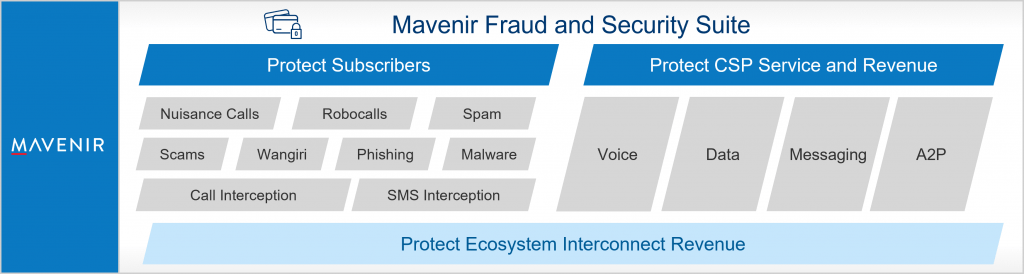
Mavenir’s SpamShield technology protects the CSPs’ subscribers against spam, scams, malware, phishing and fraud and provides A2P revenue protection for the carrier.
SpamShield’s innovative technology uses real-time AI and machine learning technology with unique message fingerprinting algorithms that enable automatic detection of messaging fraud scenarios.
